
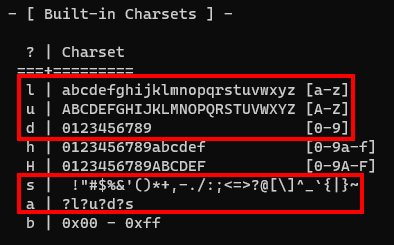
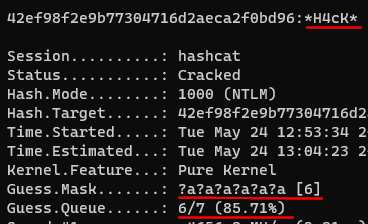
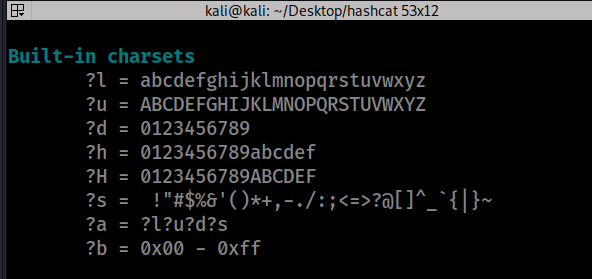
Why would you use masks with hashcat when you crack hashes in brute force mode. @hashcat #LINUX4HACKERS #HASHCAT #LINUX #INFOSEC #HACKING #PENTEST #PENTESTING #REDTEAM #NVIDA #TESLAM60 #NTLM #BRUTEFORCE – Tips and Tricks

Why would you use masks with hashcat when you crack hashes in brute force mode. @hashcat #LINUX4HACKERS #HASHCAT #LINUX #INFOSEC #HACKING #PENTEST #PENTESTING #REDTEAM #NVIDA #TESLAM60 #NTLM #BRUTEFORCE – Tips and Tricks

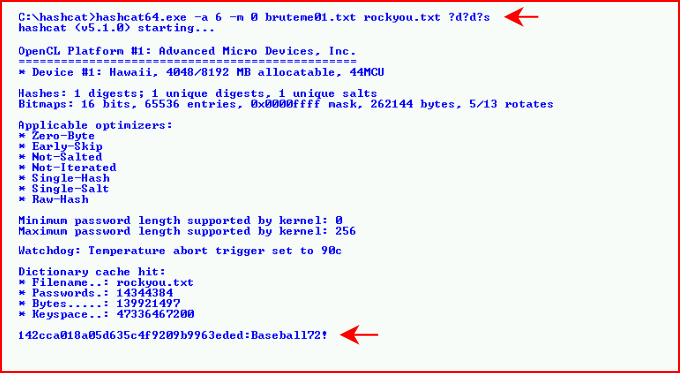
Cracking WPA2 WPA with Hashcat in Kali Linux (BruteForce MASK based attack on Wifi passwords) - Page 3 of 3 - blackMORE Ops

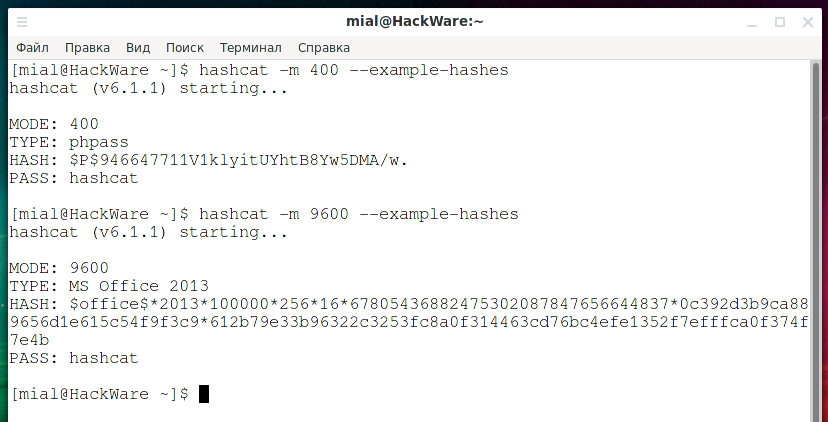




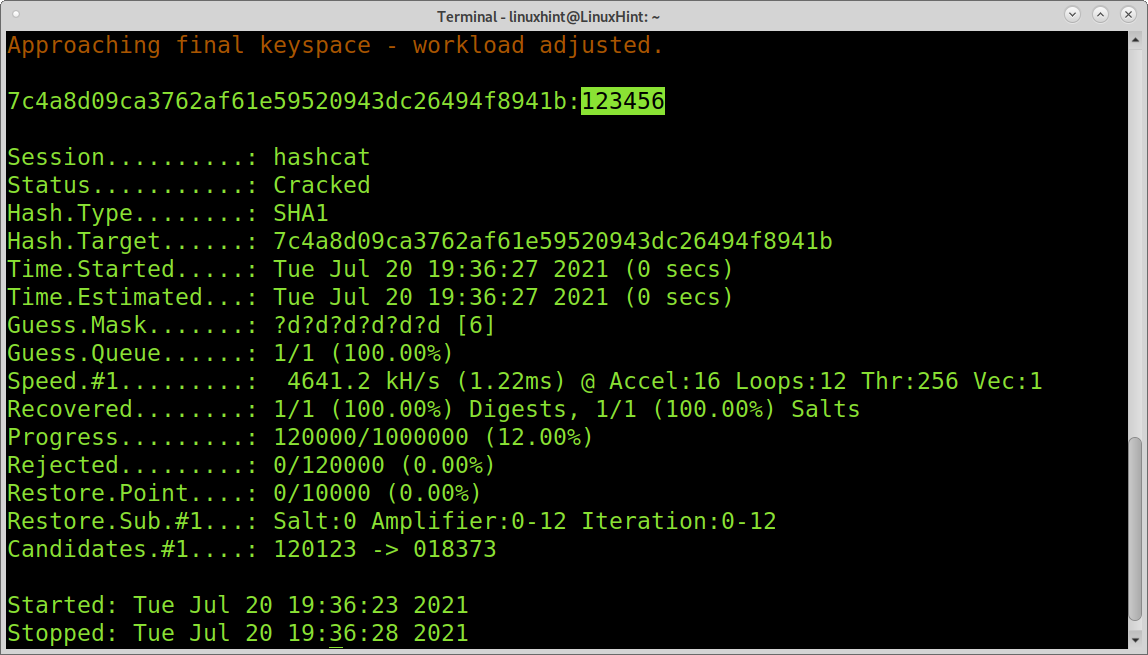



![Hashcat tutorial for beginners [updated 2021] | Infosec Resources Hashcat tutorial for beginners [updated 2021] | Infosec Resources](https://resources.infosecinstitute.com/wp-content/uploads/2018/04/122120-2.png)